Need Help?
Please Feel Free To Contact Us. We Will Get Back To You With 1-2 Business Days.
Phone : 1-443-482-6120
Email: contact@serigor.com
Quick Contact
GOVERNANCE AND RISK MANAGEMENT – CENTRALISED, PRIORITIZED, AND AUDITABLE RISK MANAGEMENT
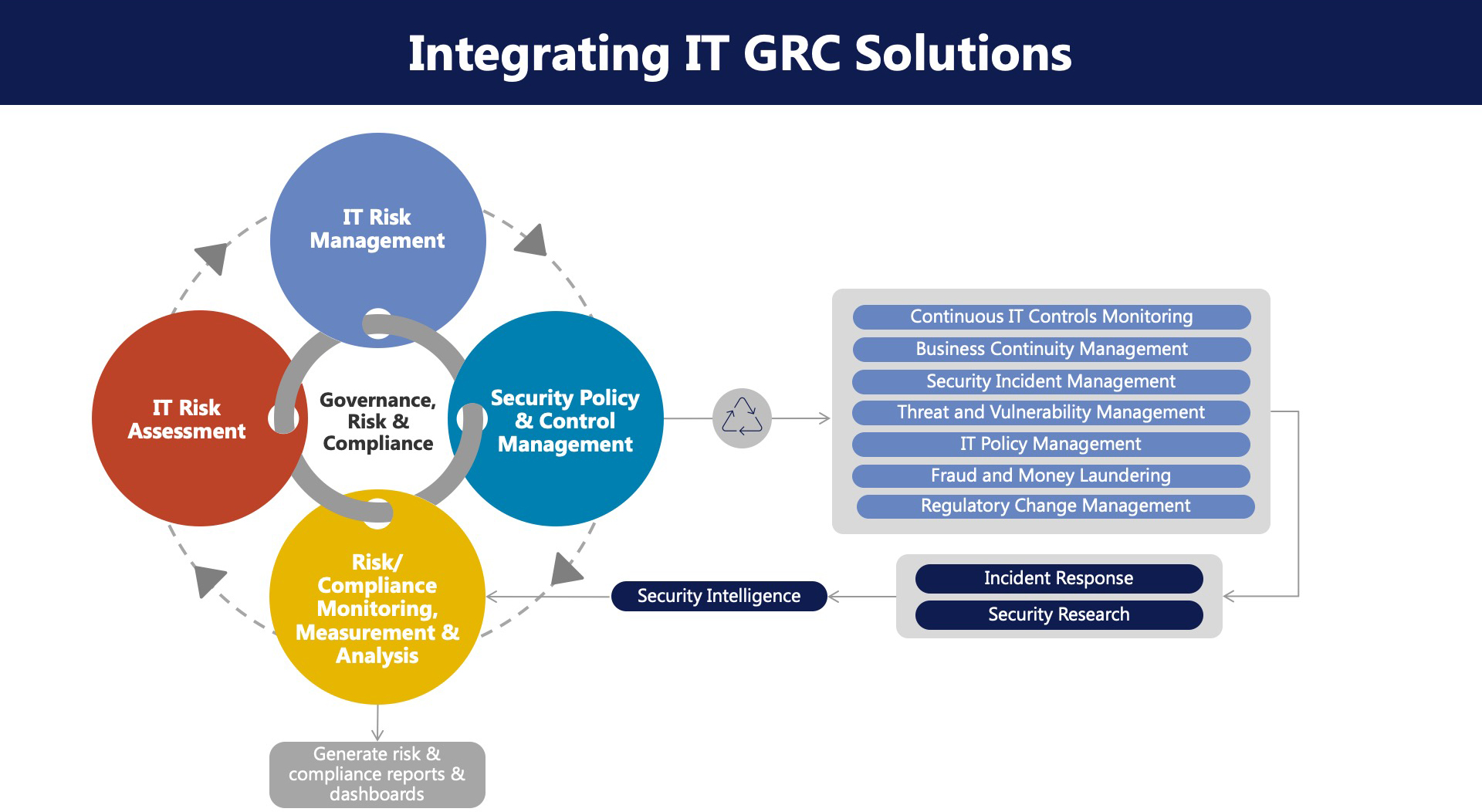
Serigor’s approach to Governance, Risk, and Compliance is based on the industry best practices supported by the CMMI standards. Our Governance, Risk, and Compliance Framework—is a set of practices and measures to help clients achieve business objectives, address uncertainty, and act with integrity. The risk landscape is uncertain and interconnected. Identifying risks means recognizing potential conditions, activities, or decisions that may jeopardize project success. Identifying issues means recognizing existing conditions, activities, or decisions that are impacting project success.
The risk assessment consists of determining the likelihood and the severity of threats and vulnerabilities. Not all threats are equal—some happen more often than others, and others are more devastating to the organization. The first step Serigor takes in identifying the worst threats is to find out how likely the threat will occur. Next, quantify the impact the threat could have on the enterprise. Then, by mapping threats and vulnerabilities, likelihood, and impact to critical information, processes, and information assets, we determine a scale to rate the severity of the consequences of an event or a breach in security. This will help determine which threats or vulnerabilities we need to prepare for.
Serigor can assist in identifying, monitoring, developing, and managing risks in addition to managing the optimized utilization of people, process, and technology to enhance Governance, Risks, and Compliance effectiveness and help in cost savings.
Our risk assessment framework not only provides realistic results but also supports in implementing and remediating measures that are sustainable and reusable.

There are three measures Serigor Risk Assessment Team will help in :
Preventive :
Mitigation :
Recovery :
Benefits :
- Improved risk and control assurance through a more robust, effective, and shortened auditing process.
- Clear and concise governance documentation that enables effective security awareness.
- Increased management satisfaction through accurate and timely reporting of significant KPIs for strategic planning and rapid decision-making.
- Automation and streamlined processes to enhance efficiency and effectiveness.
Learn about our hiring and consulting options
Call Us Now 1-443-482-6120
